Global Cybersecurity Outlook 2025: Key Threats and Resilience Strategies
Look, I’ll be straight with you. The cybersecurity landscape heading into 2025 isn’t just challenging – it’s downright terrifying. We’re not talking about your garden-variety phishing emails anymore. The threats we’re facing are sophisticated, relentless, and frankly, they’re evolving faster than most organizations can keep up.
As someone who’s been tracking these trends, I can tell you that what we’re seeing isn’t just another cycle of incremental improvements in attack methods. We’re witnessing a fundamental shift in how cybercriminals operate, and honestly? Most businesses aren’t ready for what’s coming.
The Storm Clouds Gathering: What’s Actually Coming for Us
AI That Fights Back
Here’s where things get really interesting (and scary). We’ve all been talking about AI automation transforming business operations, but cybercriminals are getting the same memo. By 2025, we’re looking at malware that doesn’t just follow pre-programmed instructions – it learns, adapts, and literally thinks on its feet.
Imagine a piece of malware that studies your network defenses in real-time, then develops custom attack strategies just for your environment. That’s not science fiction anymore. The latest cybersecurity research suggests these autonomous AI attacks will become mainstream within the next two years.
And deepfakes? They’re reaching a level of sophistication that’s genuinely disturbing. We’re talking about synthetic videos and audio so realistic that even forensic experts struggle to spot the fakes. For identity theft and corporate espionage, this is a game-changer.
Supply Chains: The Weakest Link Gets Weaker
Remember SolarWinds? That was just the appetizer. The main course is coming, and it’s going to be brutal. Our interconnected business world means that when one link breaks, the whole chain can come crashing down.
What’s particularly concerning is how attackers are moving beyond software. They’re now targeting hardware components, firmware, and even the third-party cloud services that power most modern businesses. It’s like having a security system that locks the front door while leaving every window wide open.
IoT Explosion: More Devices, More Problems
Every smart device added to our networks is another potential entry point for attackers. And we’re not just talking about smart thermostats here. IoT resource management has become critical as billions of connected devices flood our infrastructure.
Smart cities, industrial control systems, connected vehicles – they’re all fair game. The scary part? Many of these devices were designed with convenience in mind, not security. And once they’re deployed, updating their security is often impossible or prohibitively expensive.
According to industry reports, attackers are increasingly targeting critical infrastructure through these IoT vulnerabilities, with potentially catastrophic real-world consequences.
Ransomware Gets a Makeover
Forget everything you think you know about ransomware. The “encrypt your files and demand payment” model is so 2020. Modern ransomware operators are running sophisticated business models that would make legitimate corporations jealous.
They’re combining data encryption with exfiltration, threatening to release sensitive information publicly if ransom demands aren’t met. But it gets worse – they’re specifically targeting critical services and infrastructure, where downtime isn’t just inconvenient, it’s potentially life-threatening.
Nation-States Playing Dirty
Geopolitical tensions are spilling over into cyberspace in ways we’ve never seen before. Nation-state actors aren’t just stealing secrets anymore – they’re actively disrupting services, manipulating public opinion, and testing the limits of what they can get away with.
The attribution problem makes this particularly challenging. When a cyberattack happens, proving who was actually behind it is incredibly difficult, giving state actors a degree of plausible deniability that they’re exploiting ruthlessly.
Fighting Back: Strategies That Actually Work
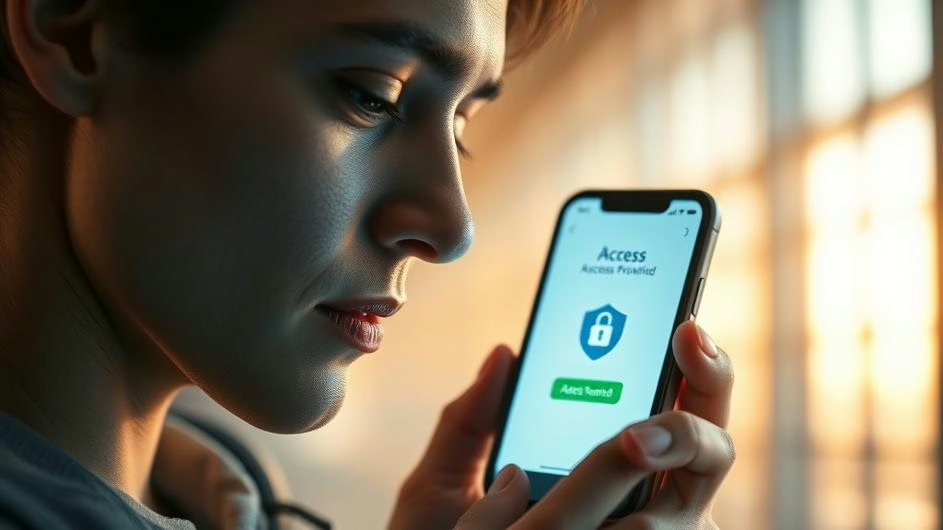
Zero Trust: Trust Nobody, Verify Everything
The old “castle and moat” security model is dead. Period. If you’re still operating under the assumption that anything inside your network is trustworthy, you’re setting yourself up for disaster.
Zero Trust isn’t just a buzzword – it’s a fundamental shift in how we think about security. Every user, every device, every application needs to be verified continuously. It’s more work upfront, but it’s the only approach that makes sense in today’s threat landscape.
Proactive Hunting Instead of Reactive Hoping
Waiting for your security tools to alert you to a breach is like waiting for someone to tell you your house is on fire. By then, it’s often too late. Smart organizations are investing in threat hunting teams that actively search for signs of compromise before the attackers announce themselves.
This means integrating real threat intelligence, not just generic feeds, and using AI agents for enhanced security operations to process and analyze the massive amounts of data flowing through modern networks.
Building a Security-First Culture
Here’s something that might surprise you: your biggest security vulnerability probably isn’t your technology – it’s your people. And I don’t mean that in a blame-the-user way. I mean that creating a genuine security-first culture requires investment, training, and leadership commitment that most organizations simply haven’t made.
Effective security awareness isn’t about showing people scary videos about phishing emails once a year. It’s about making security considerations a natural part of how everyone thinks about their work.
Beyond Backups: Real Incident Response
Let’s be honest – you’re going to get breached. The question isn’t if, it’s when. And when that happens, having a robust incident response plan isn’t just helpful, it’s essential for survival.
This goes way beyond having backups (though those are crucial too). We’re talking about forensic capabilities, legal strategies, communication plans, and recovery procedures that have been tested under pressure. Understanding how hackers operate is crucial for building effective response capabilities.
Security by Design, Not as an Afterthought
If you’re building applications or infrastructure and thinking “we’ll add security later,” you’ve already lost. Security needs to be baked into every phase of development, from initial design through deployment and maintenance.
DevSecOps isn’t just a trendy acronym – it’s a practical approach that catches vulnerabilities early when they’re cheap and easy to fix, rather than after they’ve been deployed to production.
Preparing for the Quantum Future
Quantum computing capable of breaking current encryption might still be years away, but smart organizations are already preparing. The transition to quantum-resistant cryptography is going to be massive, and starting early means avoiding a panic migration later.
The Bottom Line: What This Means for You
The cybersecurity challenges of 2025 aren’t going to be solved by buying more security tools or hiring a few more analysts. They require fundamental changes in how we think about risk, how we design systems, and how we prepare for the inevitable.
The global cybersecurity outlook makes it clear that organizations that take a proactive, comprehensive approach to security will weather the storm. Those that don’t? Well, let’s just say 2025 might be a very expensive year for them.
International cooperation, investment in cutting-edge defensive technologies, and addressing the cybersecurity talent shortage aren’t just nice-to-haves anymore – they’re survival imperatives. The organizations that understand this and act accordingly will thrive. The rest will become cautionary tales.
The digital world is expanding relentlessly, and cybersecurity remains the foundation everything else is built on. The 2025 cybersecurity outlook isn’t just a prediction – it’s a call to action. The question is: are you ready to answer it?
Sources:
- Embedding Project – Global Cybersecurity Outlook 2025
- IFMA Knowledge Library – Global Cybersecurity Outlook 2025
- Drishti IAS – Global Cybersecurity Outlook 2025 Analysis
- Industrial Cyber – WEF Global Cybersecurity Outlook 2025 Report
- EY – Global Cybersecurity Outlook 2025